
Researchers have connected the comparatively new Ransom Cartel ransomware operation with the infamous REvil gang dependent on code similarities in both of those operations’ encryptors.
REvil achieved its pinnacle of success in the first fifty percent of 2021, compromising hundreds of firms in a Kaseya MSP supply-chain attack, demanding a $50 million payment from personal computer maker Acer, and extorting Apple using stolen blueprints of non-nevertheless-introduced units.
The REvil ransomware gang finally shut down in Oct 2021 following intense stress from law enforcement. On the other hand, in January 2022, the Russian authorities announced arrests, funds seizures, and charges against 8 of the gang’s associates.
In December 2021, a new ransomware procedure named ‘Ransom Cartel’ was introduced that shared several code similarities to REvil’s malware.
A doable rebrand?
A new report from Palo Alto Network’s Device 42 sheds further light on the relationship concerning the two cybercrime gangs, sharing similarities in techniques, ways, and treatments (TTPs) and, most importantly, widespread floor in the code of their malware.
Due to the fact the resource code of REvil’s encrypting malware was never leaked on hacking message boards, any new challenge applying comparable code is either a rebrand or a new operation released by a core member of the first gang.
When analyzing encryptors for Ransom Cartel, the researchers observed similarities in the composition of the configuration embedded in the malware, whilst the storage places are distinct.
The samples analyzed by Device 42 clearly show that Ransom Cartel is lacking some configuration values, indicating that the authors are both making an attempt to make the malware leaner or that their basis is an previously version of the REvil malware.
The encryption plan is where by the similarities come to be much better, with Ransom Cartel’s samples creating many pairs of community/private keys and session insider secrets, an REvil program that shined in the Kaseya attacks.
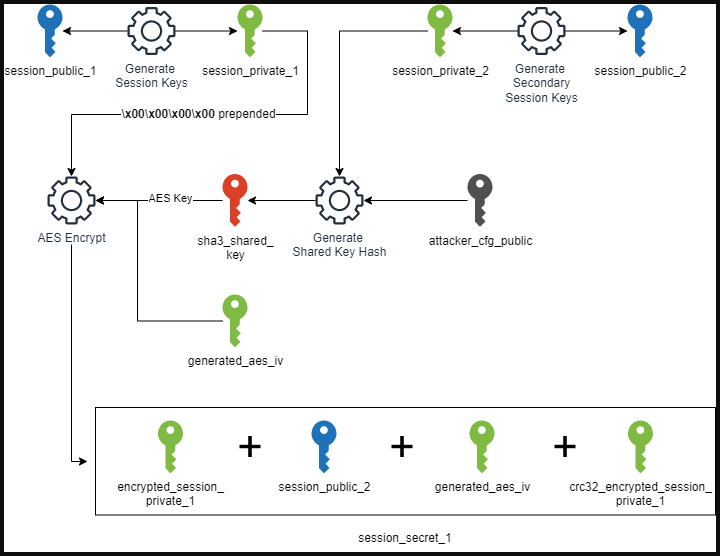
“The two use Salsa20 and Curve25519 for file encryption, and there are pretty number of discrepancies in the structure of the encryption schedule besides the composition of the interior kind structs,” clarifies the report by Unit 42 scientists Daniel Bunce and Amer Elsad.
An attention-grabbing finding is that the Ransom Cartel samples do not characteristic REvil’s powerful obfuscation, which could indicate that the authors of the new malware will not have REvil’s original obfuscation motor.
Ransom Cartel operations
There are also similarities in the ways, strategies, and treatments (TTPs) employed by REvil and Ransom Cartel, these types of as double-extortion attacks, big ransom calls for, and a knowledge leak site to stress victims into paying out a ransom.
Nonetheless, one technique applied by Ransom Cartel, and not noticed in REvil attacks, is making use of the Home windows Details Protection API (DPAPI) to steal qualifications.
For this approach, Ransom Cartel employs a software named “DonPAPI,” which can search hosts for DPAPI blobs made up of Wi-Fi keys, RDP passwords, and credentials saved in internet browsers and then down load and decrypt them regionally on the device.
These qualifications are then made use of to compromise Linux ESXi servers and authenticate to their vCenter world wide web interfaces.
Last but not least, the danger actors shut down VMs, terminate all relevant processes, and encrypt Vmware-similar files (.log, .vmdk, .vmem, .vswp and .vmsn).
The existence of DonPAPI, a not normally made use of tool, suggests that the operators of Ransom Cartel are knowledgeable menace actors.
.png)
An additional REvil-joined ransomware procedure?
When there are strong connections between Ransom Cartel and REvil, they are not the only ransomware gang presently utilizing REvil’s code.
In April 2022, another ransomware procedure we simply call ‘BlogXX’ was observed, whose encryptors were being pretty much similar to the REvil encryptors.
Scientists at the time advised BleepingComputer that the BlogXX encryptor was not only compiled from REvil’s supply code but also bundled new changes.
“Indeed, my evaluation is that the menace actor has the resource code. Not patched like “LV Ransomware” did,” security researcher R3MRUM informed BleepingComputer at the time.
AdvIntel CEO Vitali Kremez also instructed BleepingComputer that BlogXX’s encryptors incorporated a new ‘accs’ configuration option that contained account credentials for the focused victim.
On top of that, the new ransomware operation employed identical ransom notes and called by themselves ‘Sodinokibi,’ an alternate title for REvil, on their Tor payment sites.
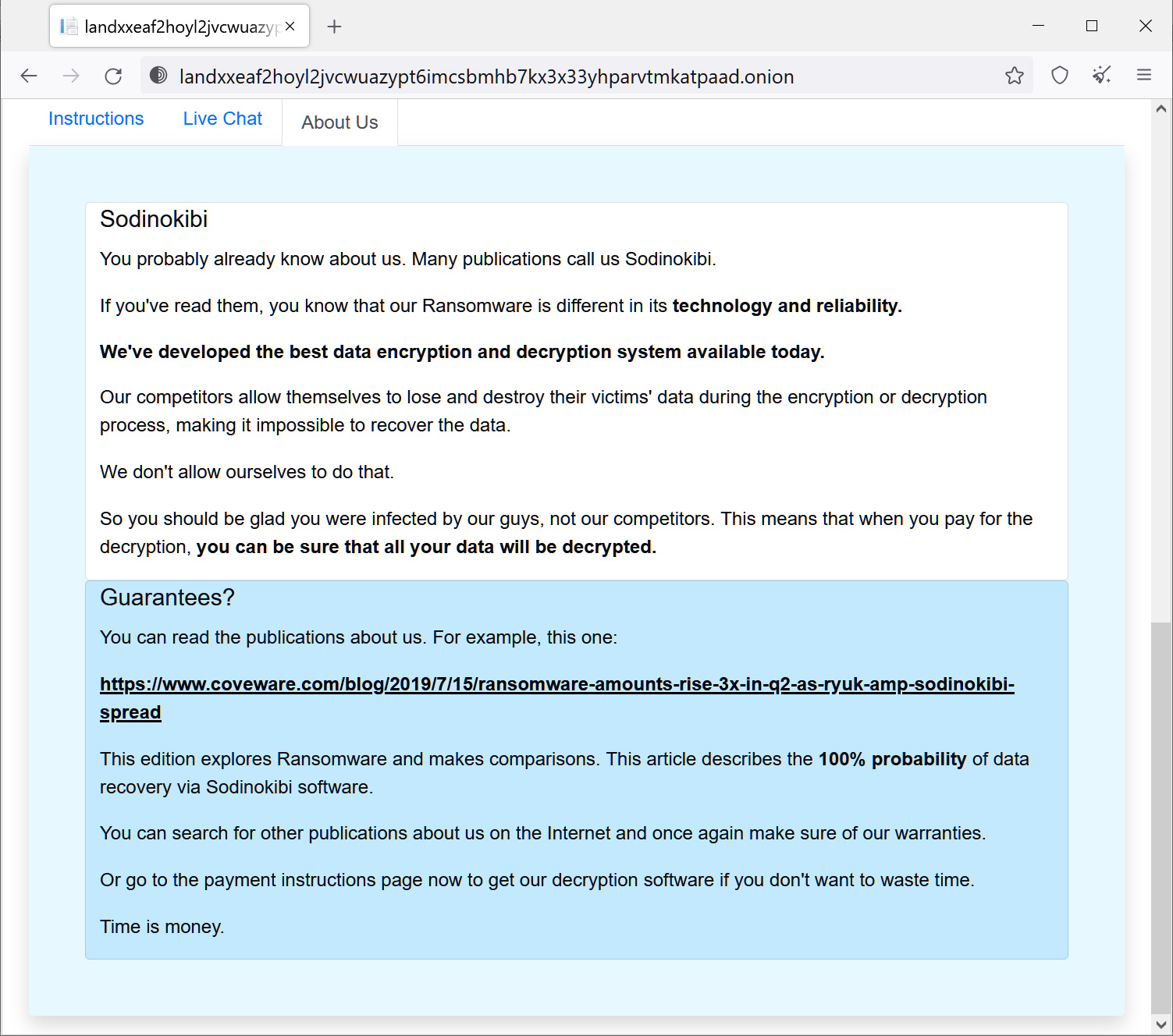
Resource: BleepingComputer
However, as opposed to Ransom Cartel, BlogXX’s history has an additional element that lends robust proof that they are, in point, the REvil rebrand.
Following REvil’s shut down, the gang’s previous Tor sites had been revived, but this time redirected guests to the BlogXX operation’s information leak website.
Whilst these websites appeared practically nothing like REvil’s prior web-sites, the point that the outdated Tor web pages were being redirecting to BlogXX’s web sites confirmed that the new procedure experienced handle of REvil’s Tor private keys.
As only the unique REvil operators would have these Tor private keys, it showed a sturdy link among the two gangs.
When irrefutable proof that BlogXX or Ransom Cartel are rebrands of the REvil operation is nonetheless to be identified, it’s rather clear that at minimum some of the first users are behind these new ransomware operations.




